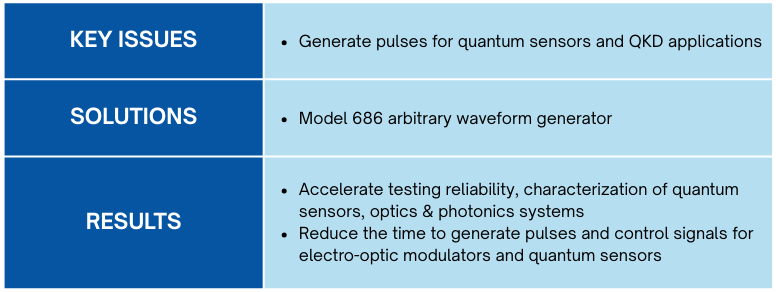
Introduction
In our digital age, sensitive information from financial transactions to classified government data flows through networks at an unprecedented rate. However, conventional encryption methods that rely on mathematical algorithms face an existential threat from quantum computers.
Quantum computers could easily crack these encryption codes when they become powerful enough. This encapsulates the urgency to develop quantum-resistant encryption methods. QKD stands at the forefront of this endeavor.
The laws on quantum mathematics are not only used to protect our communications and data, but also to understand the world around us at an unprecedented level of detail. Light, temperature, pressure, heat, and other things that are imperceptible to more traditional sensors can be measured by quantum sensors. The quantum sensors depend on the constants of nature and their reliability never degrades; they are self-calibrating and their measurements don’t drift off over time like traditional sensors do.
High performance AWGs like the Model 686 are becoming extremely popular in designing and developing these emerging breakthrough technologies.
QKD: Quantum Key Distribution
Quantum Key Distribution (QKD) is a secure communication method for exchanging encryption keys only known between shared parties. It uses properties found in quantum physics to exchange cryptographic keys in such a way that is provable and guarantees security. QKD enables two parties to produce and share a key that is used to encrypt and decrypt messages. Specifically, QKD is the method of distributing the key between parties.
Key distribution on a conventional scale relies on public key ciphers that use complicated mathematical calculations requiring a prohibited amount of processing power to break. The viability of public key ciphers, however, faces several issues such as the constant implementation of new computing power. In addition, quantum computing will render most of today’s public key encryption strategies unsafe.
QKD is different from conventional key distribution because it uses a quantum system that relies on basic and fundamental laws of nature to protect the data, rather than relying on mathematics.
QKD works by transmitting many light particles or photons over fiber optic cables between parties. Each photon has a random quantum state, and collectively, the photons sent make up a stream of ones and zeros. This stream of ones and zeroes are called qubits, and they are the equivalent of bits in a binary system. When a photon reaches its receiving end it travels through a beam splitter, which forces the photon to randomly take one path or another into a photon collector.
The receiver then responds to the original sender with data regarding the sequence of the photons sent and the sender then compares that with the emitter, which would have sent each photon.
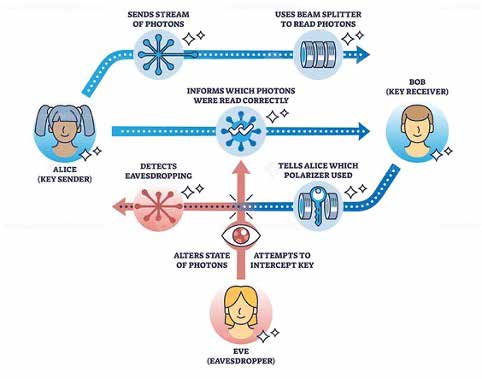
Figure 1: Alice, Bob, and Eve
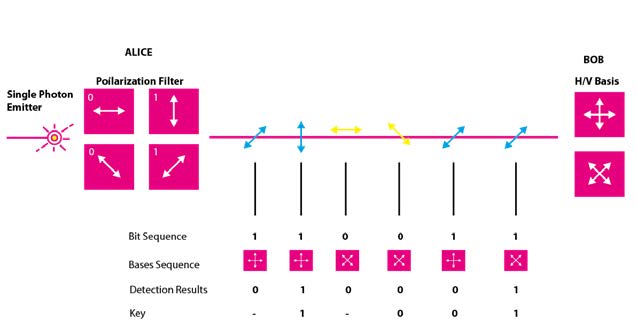
Figure 2: Alice and Bob transmitting photons
Photons in the wrong beam collector are discarded; what’s left is a specific sequence of bits. This bit sequence can then be used as a key to encrypt data; any errors and data leakage are removed during a phase of error correction and other post-processing steps.
To do this Alice sends photons to Bob. Photons are the smallest part of the light. Since photons are not only particles but also waves, they oscillate. They can oscillate in different directions; when they oscillate in only one direction, they are called polarized.
Polarizing filters enable us to filter photons. Then, for example, only the photons that oscillate up and down can pass through; these are called vertically polarized. Quantum mechanics has even made it possible to send single photons. Alice sends polarized photons to Bob and the light passes through if Bob holds his filter the same way as the photons polarized by Alice.
On the other hand, if he holds his filter crosswise to the direction of the polarization, no photon passes through. This means that each photon can be measured only once.
What happens if Bob turns his filter diagonally just a little bit towards Alice’s polarization direction? Sometimes a photon can pass through the filter and sometimes not; if both polarize diagonally in the same direction, the photons all pass through again. In the case that they polarize in different diagonal directions, the photons no longer pass through Bob’s filter.
Quantum Key Exchange (QKD)
Alice makes notes of the polarization with which she sent the photons off and Bob makes a note of how he held his filter and whether light was received or not. Now the two can talk publicly about how Alice polarized her photons and how Bob held his filter. Everyone can hear this. Whenever one person uses the filter diagonally and the other vertically or transversely – this part gets deleted; from the remaining ones they build their key.
If an attacker (man-in-the-middle) called Eve tries to read along a photon with a polarization filter, she has to send a new photon to Bob afterwards. Eve does not know if she has held the filter correctly: if she doesn’t see any light, she could have held her filter crosswise to Alice’s filter or just slightly differently, but the photon didn’t get through. If she does see light, it could still be because the photon came through with the filter slightly rotated, so she may still have held the filter incorrectly. Eve doesn’t know if holding the filter diagonally was correct or not.
Photons cannot be copied and can only be measured once, so Eve must guess quite often what she sends on to Bob. Alice and Bob only talk later about how they used their filters and which parts they can use for their key.
However, Eve must decide beforehand whether she was correct with diagonal or non-diagonal, but without the public conversation she must guess how to proceed. Thus, Eve often makes mistakes. Bob makes as many mistakes as Eve, but his are simply deleted. Before Alice and Bob build their key they compare individual digits.
They don’t use them for the key afterwards, but if they don’t match they know that someone has been listening, so the quantum encryption is used to agree on a key. Since the method is based on the randomness of quantum mechanics, whether photons can pass through slightly twisted filters or not is considered unbreakable.

Figure 3: Quantum Encryption
Types of QKD
There are many different types of QKD, but two main categories are prepare-and-measure protocols and entanglement-based protocols.
Prepare-and-measure protocols focus on measuring unknown quantum states. They can be used to detect eavesdropping, as well as how much data was potentially intercepted.
Entanglement-based protocols focus on quantum states in which two objects are linked together, forming a combined quantum state. The concept of entanglement means that measurement of one object thereby affects the other. If an eavesdropper accesses a previously trusted node and changes something, the other involved parties will know. By implementing quantum entanglement or quantum superpositions, just the process of trying to observe the photons changes the system, making an intrusion detectable.
It is difficult to implement an ideal infrastructure for QKD. It is perfectly secure in theory, but in practice, imperfections in tools such as single photon detectors create security vulnerabilities. It is important to keep security analysis in mind.
Modern fiber optic cables are typically limited in how far they can carry a photon. The range is often upward of 100 km. Some groups and organizations have managed to increase this range for the implementation of QKD. The University of Geneva and Corning Inc. worked together, for example, to construct a system capable of carrying a photon 307 km under ideal conditions.
Another challenge of QKD is it relies on having a classically authenticated channel of communications established. This means that one of the participating users already exchanged a symmetric key in the first place, creating a sufficient level of security. A system can already be made sufficiently secure without QKD through using another advanced encryption standard. As the use of quantum computers becomes more frequent, however, the possibility that an attacker could use quantum computing to crack into current encryption methods rises, making QKD more relevant.
QKD Attack Methods
Even though QKD is secure in theory, imperfect implementations of QKD have the potential to compromise security. Techniques for breaching QKD systems have been discovered in real-life applications. For example, even though the BB84 protocol should be secure, there is currently no way to perfectly implement it. The phase remapping attack was devised to create a backdoor for eavesdroppers. The attack takes advantage of the fact that one party member must allow signals to enter and exit their device. This process takes advantage of methods used widely in many commercial QKD systems.
Another attack method is the photon number splitting attack. In an ideal setting, one user should be able to send one photon at a time to the other user. However, most of the time, additional similar photons are sent. These photons could be intercepted without either party knowing. To combat this type of attack, an improvement to the BB84 protocol was implemented called decoy state QKD. This protocol uses a set of decoy signals mixed in with the intended BB84 signal while enabling both parties to detect if an eavesdropper is listening.
QKD Implementation Methods
There are two different approaches to implement QKD: one focuses on discrete variables (DV-QKD) and relies on single photons with encoded random data. The other one plays on the wave nature of light with information encoded in the quadrature of its electromagnetic fields – continuous variables (CV-QKD). Coherent homodyne or heterodyne detection is used to continuously retrieve the quadrature value of the signal to read the key into it.
In the market there are different modulation solutions for the transmitter side of the communication (Alice) and for the receiver side (Bob) optical hybrid demodulators can be used. One of the most technologically advanced intensity modulators is the Exail NIR-MX800: the intrinsic and unparalleled benefits of LiNbO3 modulation offers high bandwidth, high contrast and ease of use.

Figure 4: Electro-optic modulator
The Model 686 and Model 685 series allow controlling directly to those kinds of Electro-Optic Modulators and to generate very short optical pulses. The unique features of generating pulse with 50 ps rise/fall time, 100 ps pulse width and 5Vpp amplitude offers the solution of driving the EOM without using an external amplifier.
Figure 5: BNC Model 686
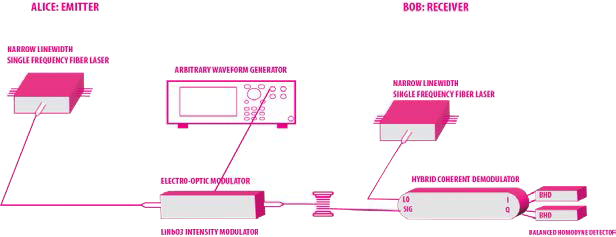
Figure 6: Short optical pulse generation with the Model 686
The diagram above represents a typical connection to the Model 686 with a first modulation block used to generate short optical pulses. For example, using Exail’s NIR-MX800 and the BNC Model 686, very short optical pulses width from 100 ps can be achieved at 850 nm, 1310 nm and 1550 nm respectively. It is important to note that in the connection diagram between the Model 686 and the Intensity Modulator, an external amplifier is not used. This is because the Model 686 can generate very narrow pulses of 100 ps width at full amplitude 5Vpp like in the pictures below.
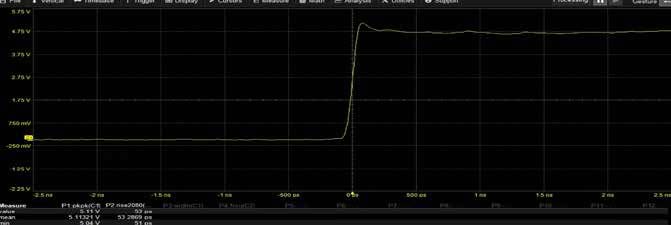
Figure 7: 50 ns rise time @ 5 Vpp

Figure 8: 100 ns pulse width @ 5 Vpp
Quantum Sensors

Quantum sensors allow us to understand the world around us at an unprecedented level of detail: their advanced sensor technology vastly improves the accuracy of how we measure, navigate, study, explore, see, and interact with the world around us by sensing changes in motion, and electric and magnetic fields. The data is collected at the atomic level. Collecting these “delicate” data at the atomic level often means extracting information from individual atoms instead of from the huge collections of atoms, as happens in classical physics.
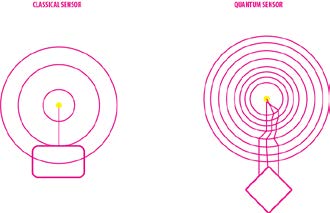
Figure 9: classical and quantum sensors
This allows quantum sensors to make our technological devices exponentially more accurate, more thorough, more efficient, and more productive. Another great benefit is that devices that use quantum sensing are not subject to the same physical constraints as conventional sensors. This allows for exceptional reliability with less vulnerability to the signal jamming and other electromagnetic interference that is increasingly common with today’s light- and sound-based data sensors.
Since quantum sensing measures activity in the physical world using atomic properties, they can be of great use in the following applications:
- Faster, more accurate, and more reliable geolocation than is possible with today’s satellite-dependent global positioning system (GPS) devices, with far fewer limitations
- Providing doctors with more detailed and accurate medical diagnostic images at lower cost and with fewer potential side effects for patients
- Better, safer autonomous navigation of vehicles on the ground, in the air, and at sea – even in high traffic areas and around unexpected obstacles
- More accurate and less vulnerable guidance systems in space, under water, and in the increasing number of zones overwhelmed by radio-frequency (RF) signals
- Reliable detection, imaging, and mapping of underground environments from transit tunnels, sewers, and water pipes to ancient ruins, mines, and subterranean habitats
- Deeper, more active sensing of gravitational changes and tectonic shifts that can forewarn or trigger avalanches, earthquakes, volcanic eruptions, tsunamis, or climate change activities
Magnetic Resonance Imaging
MRI quantum sensors have been around for decades. For example, MRI machines use quantum sensors and have been around since the 1970s. Inside one of these machines the very atoms in your body are turned into individual quantum sensors.
MRIs use magnetic fields to manipulate a quantum property called spin within your body’s atoms, and the response of those spins to the magnetic field can be measured and transformed into an image.

Figure 10: MRI machine
Atomic clocks are another kind of quantum sensor and have been around since the 1950s. They keep time in GPS satellites and even define the official SI Atomic Clock unit of a second, but things have changed since then.
Modern innovations are making new quantum sensors and applications possible: one of these newer technologies makes use of nitrogen vacancy centers, or NV centers, which can be found or fabricated within diamonds.
Pure diamond consists of a perfect lattice of carbon atoms. If two of those adjacent carbons are removed and one is replaced with a nitrogen atom, then the nitrogen together with the hold or vacant spot function as an incredibly sensitive magnetometer.
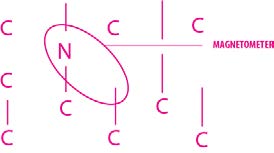
Figure 11: Magnetometer
That magnetometer uses electron spin to detect tiny changes in magnetic fields. In fact, NV centers are sensitive enough to detect changes that are 50 million times smaller than the strength of Earth’s magnetic field. And even more impressive is that they can accurately detect those tiny changes despite the presence of the Earth’s magnetic field in the background.
A diamond is a collection of carbon atoms, each bonded to four other carbons to form an orderly crystalline array. But sometimes there’s a glitch in the matrix: a stray atom of another element finds its way in, or a carbon atom is missing which leaves an empty space. These defects cause a diamond to sparkle in different hues and are called color centers.
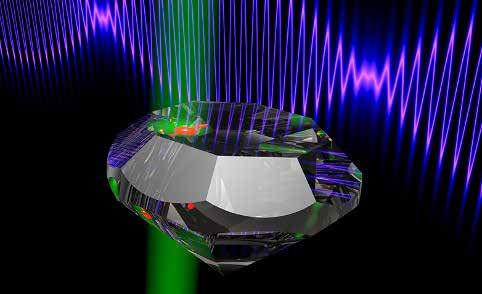
Figure 12: nitrogen-vacancy center in diamond
One particularly interesting defect occurs when a carbon in the crystal is replaced by a nitrogen atom, and the adjacent carbon is missing. This defect is known as a nitrogen-vacancy (NV) center and has its own quantum spin, which can be thought of as a rotating magnet. Diamonds are mostly made of spin-neutral carbon-12 atoms, so the NV center’s spin is unaffected by that of its immediate neighbors. Since the diamond matrix is so stiff, the atoms don’t jostle enough at room temperature to nudge the spin into a different state.
The spin can be altered, however, by electromagnetic radiation or a magnetic field — a property that enables diamonds with NV centers to be used as sensors. The NV center is also photoluminescent: when lit with green light it will emit a red glow. Because the spin state of the NV center determines how strongly the diamond fluoresces, scientists can use changes in brightness to monitor changes in the center’s spin state due to microwaves or a magnetic field. By examining which frequencies cause changes in the light, researchers can even use the diamond to measure the strength of a magnetic field. This technique is called optically detected magnetic resonance.
The BNC Model 686 has been used to control the experimental pulses’ sequences used to manipulate single tin vacancy centers in diamond.
The AWG-7000 allows generating narrow electrical square pulses with high amplitude up to 5Vpp to control an electro-optical amplitude modulator in order to generate short laser pulses.
Using this mechanism, it is possible to generate optical pulses with a close to Gaussian shape exhibiting a full-width-half-maximum as narrow as 130ps.
Furthermore, the Model 686 can be used to drive an electro-optical phase modulator for generation of frequency sidebands up to about 7GHz, enabling driving of two optical transitions with phase-stable laser fields.
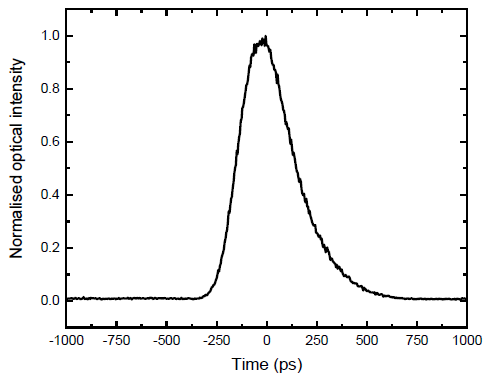
Figure 13: Gaussian pulse
The digital output channels of the BNC 686 allow control of acousto-optical amplitude modulators or they are used to generate trigger pulses for timing of experimental sequences.
In the future, it will be necessary for the real time control of the measurement protocols depending on the outcome of a certain readout within the sequence.
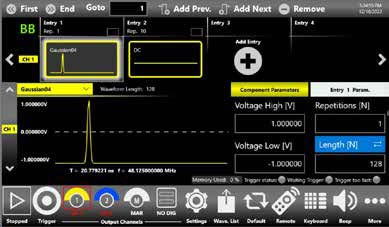
Figure 14: true-arb UI
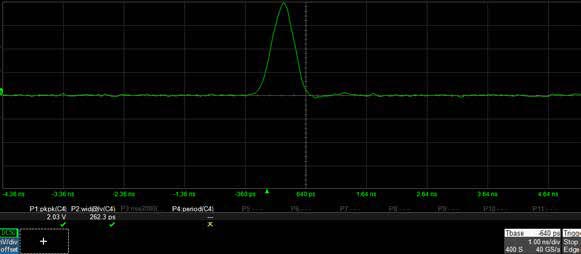
Figure 15: narrow Guassian pulse with Model 686 series